
An information-stealing malware operation named Arkanix Stealer, promoted on multiple dark web forums towards the end of 2025, was likely developed as an AI-assisted experiment.
The project included a control panel and a Discord server for communication with users, but the author took them down without notification, just two months after the operation began.
Arkanix offered many of the standard data-stealing features that cybercriminals are used to, along with a modular architecture and anti-analysis features.
Kaspersky researchers analyzed the Arkanix stealer and found clues indicating LLM-assisted development, which “might have drastically reduced development time and costs.”
Source: Kaspersky
The researchers believe that Arkanix was a short-lived project for quick financial gains, which makes detection and tracking much more difficult.
Arkanix appears online
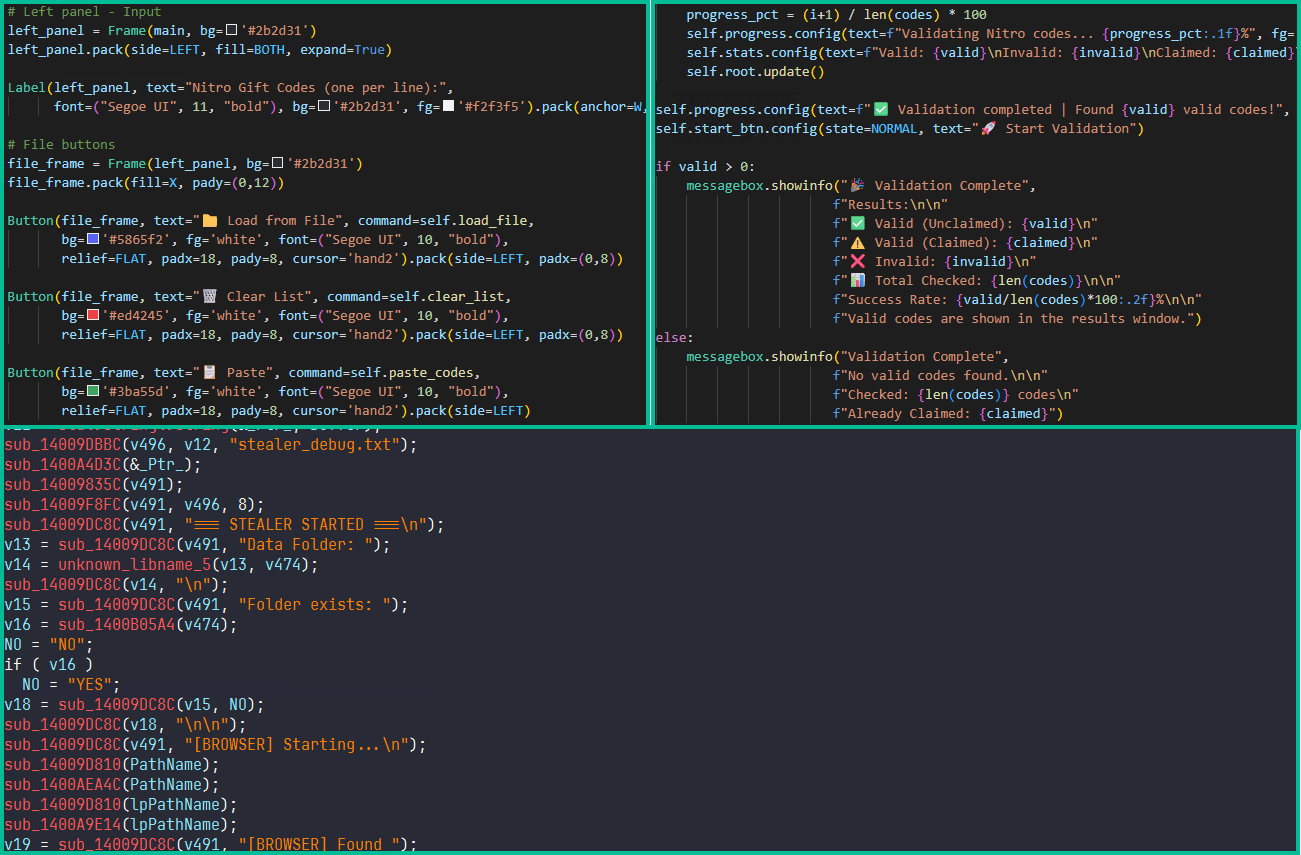
Arkanix started being promoted on hacker forums in October 2025, offering two tiers to potential customers: a basic level with a Python-based implementation, and a “premium” one with a native C++ payload using VMProtect protection, integrating AV evasion and wallet injection features.
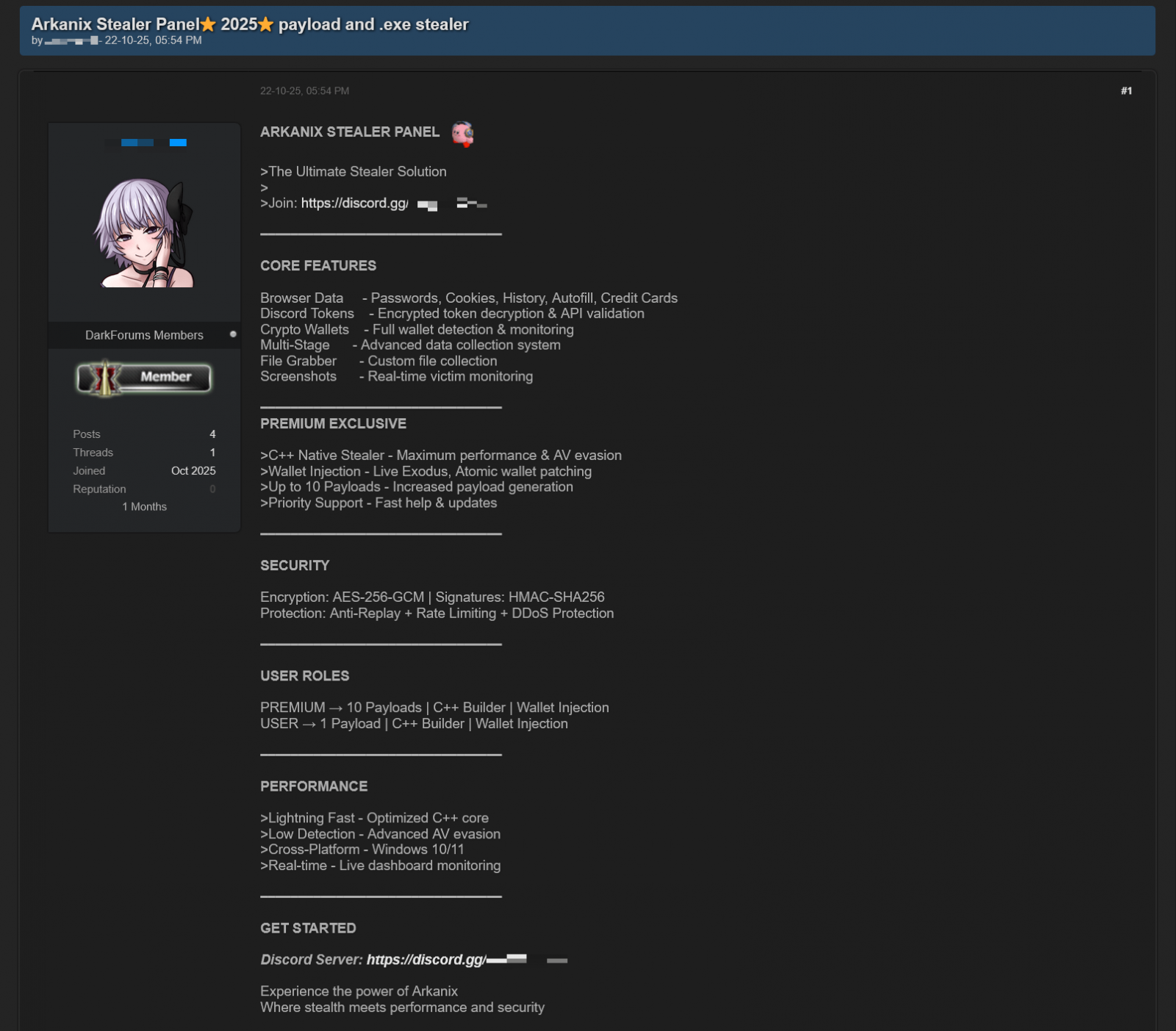
Source: Kaspersky
The developer set up a Discord server that acted as a forum for the community around the project to receive updates, provide feedback for proposed features, and receive help.
Also, a referral program was established to promote the project more aggressively, giving referrers an extra free hour of premium access, while potential new customers received one week of free access to the “premium” version.
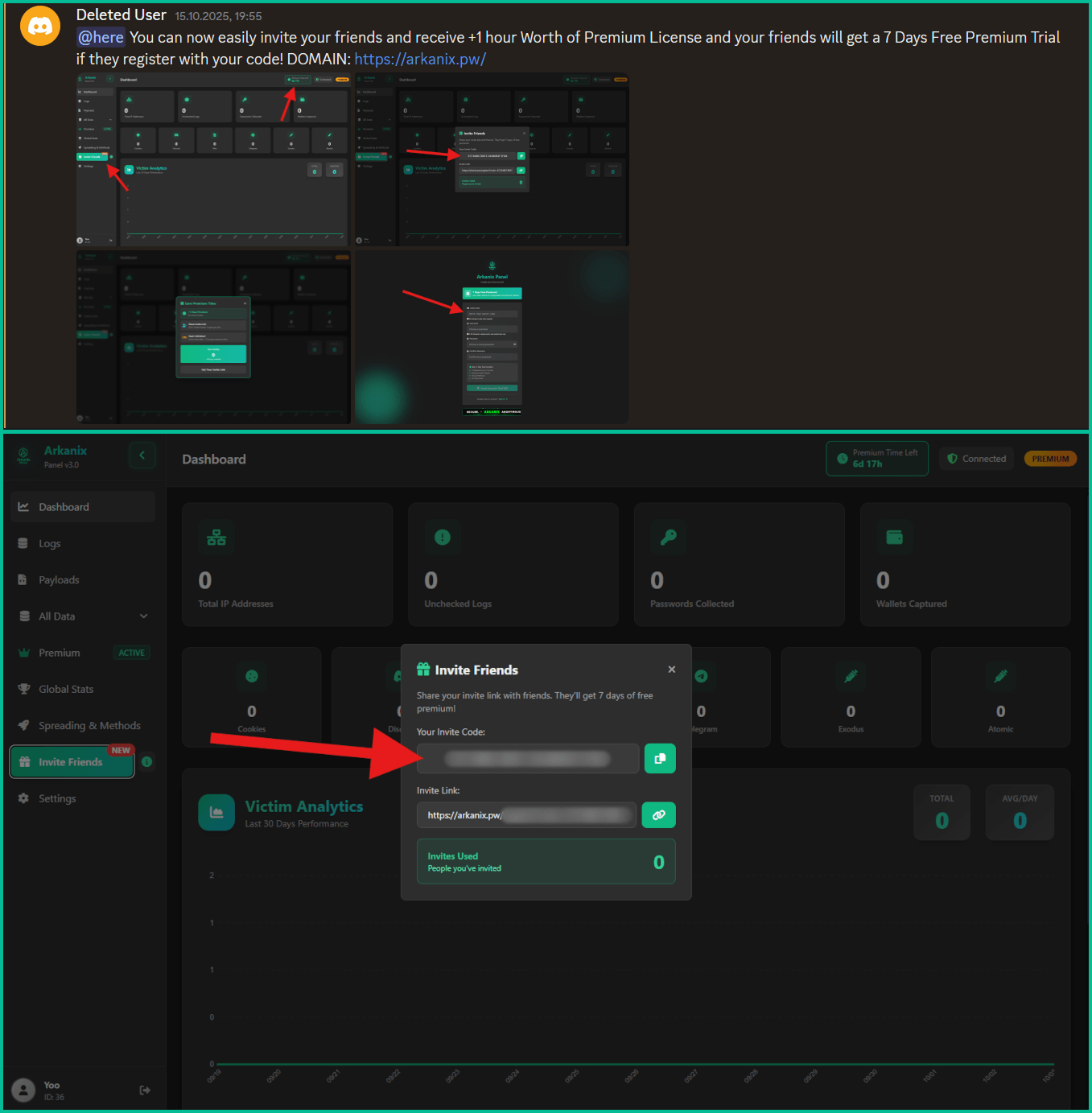
Source: Kaspersky
Data-stealing capabilities
Arkanix malware can collect system information, steal data stored in the browser (history, autofill info, cookies, passwords), and cryptocurrency wallet data from 22 browsers. Kaspersky researchers say that it can also extract 0Auth2 tokens on Chromium-based browsers.
Additionally, the malware can steal data from Telegram, steal Discord credentials, spread via the Discord API, and send messages to the victim’s friends/channels.
Arkanix also targets credentials for Mullvad, NordVPN, ExpressVPN, and ProtonVPN, and can archive files from the local filesystem to exfiltrate them asynchronously.
Additional modules that can be downloaded from the command-and-control include a Chrome grabber, a wallet patcher for Exodus or Atomic, a screenshots tool, HVNC, and stealers for FileZilla and Steam.
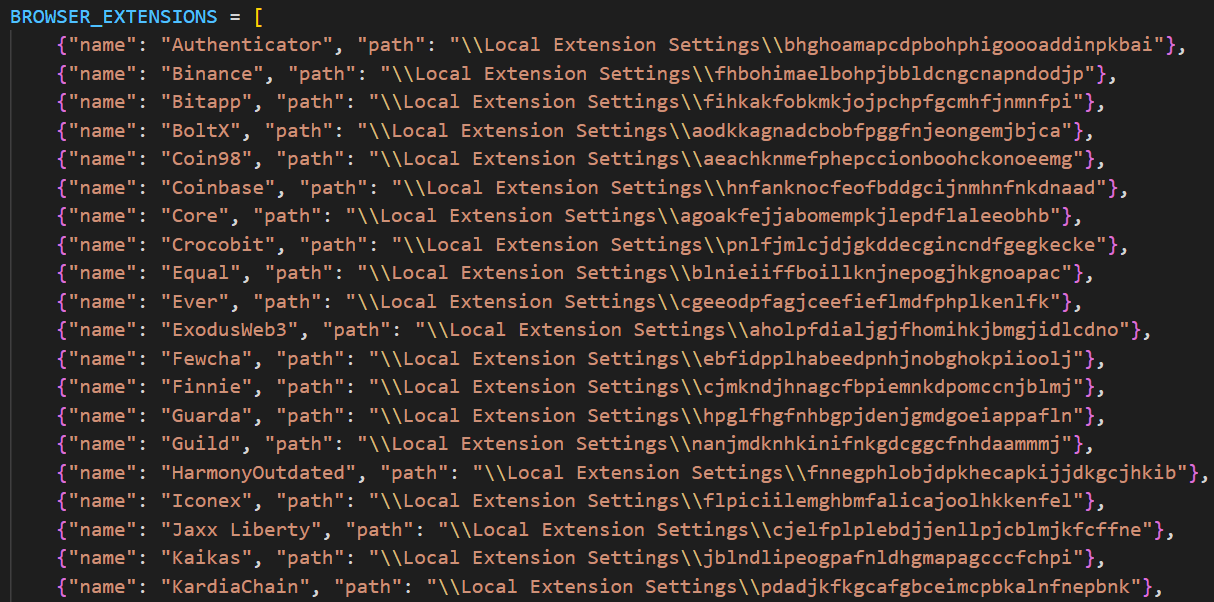
Source: Kaspersky
The “premium” native C++ version adds RDP credential theft, anti-sandbox and anti-debugging checks, WinAPI-powered screen capturing, and also targets Epic Games, Battle.net, Riot, Unreal Engine, Ubisoft Connect, and GOG.
The higher-tier variant also delivers the ChromElevator post-exploitation tool, which injects into suspended browser processes for data theft and is designed to bypass Google’s App-Bound Encryption (ABE) protection for unauthorized access to user credentials.
The purpose of the Arkanix stealer experiment remains unclear. The project may be an attempt to determine how LLM assistance can improve malware development and how quickly new features can be shipped to the community.
Kaspersky’s assessment is that Arkanix is “more of a public software product than a shady stealer.”
The researchers provide a comprehensive list of indicators of compromise (IoCs) that include hashes for detected files, along with domains and IP addresses.


