Threat actors have apparently started exploiting the newly disclosed React vulnerability tracked as React2Shell and CVE-2025-55182.
The critical vulnerability can be exploited using specially crafted HTTP requests for unauthenticated remote code execution on affected servers. It was reported to React maintainer Meta on November 29 by researcher Lachlan Davidson, and it was patched on December 3.
React2Shell may impact many systems considering that React, an open source JavaScript library designed for creating application user interfaces, powers millions of websites and its associated NPM package has millions of weekly downloads. Cloud security giant Wiz reported that 39% of cloud environments contain vulnerable React instances.
Davidson has set up a dedicated React2Shell website, but has not made public the technical details of the vulnerability. However, threat actors and researchers have been reverse-engineering the patches.
Several proof-of-concept (PoC) exploits were made public shortly after React2Shell’s disclosure, but they turned out to be fake. However, there appears to be at least one public PoC exploit that works.
Unsurprisingly, exploitation attempts have also been seen. AWS reported late on Thursday that its threat intelligence teams started seeing CVE-2025-55182 exploitation attempts by China-linked threat actors within hours of public disclosure.
AWS noted that while precise attribution is challenging due to threat actors sharing attack infrastructure, it believes attack attempts have been conducted by the groups known as Earth Lamia and Jackpot Panda.
Earth Lamia has been active since at least 2023, targeting a wide range of industries in Latin America, the Middle East, and Southeast Asia. The threat actor has been observed exploiting several vulnerabilities in its attacks.
Jackpot Panda has been around since 2020, conducting cyberespionage operations in Asia.
“Threat actors are using both automated scanning tools and individual PoC exploits,” AWS said.
Dan Andrew, head of security at Intruder, told SecurityWeek that they have also witnessed exploitation activity for React2Shell, but has not shared information on who may be behind the attacks.
Scanning and fake PoC exploits
CVE-2025-55182 is being added to vulnerability scanners and offensive security tools, which could lead to even more widespread exploitation attempts.
On the other hand, security researcher Kevin Beaumont pointed out that the vulnerability only impacts React version 19, specifically instances that use a relatively new server feature.
As Beaumont pointed out, some of these exploitation attempts are leveraging fake PoCs.
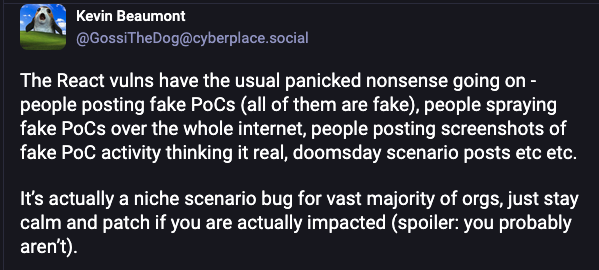
AWS confirmed that some threat actors are attempting to use the fake PoCs, which don’t work in real-world scenarios, indicating that they are desperately trying to exploit the vulnerability as quickly as possible.
However, AWS has also seen threat actors systematically troubleshooting their exploitation attempts to get them to work.
“This behavior demonstrates that threat actors aren’t just running automated scans, but are actively debugging and refining their exploitation techniques against live targets,” AWS explained.
The cloud company has made available indicators of compromise (IoCs) to help organizations detect potential exploitation attempts.
Related: Microsoft Silently Mitigated Exploited LNK Vulnerability
Related: Reporters Without Borders Targeted by Russian Hackers
