
Citrix has patched two vulnerabilities affecting NetScaler ADC networking appliances and NetScaler Gateway secure remote access solutions, one of which is very similar to the CitrixBleed and CitrixBleed2 flaws exploited in zero-day attacks in recent years.
The critical security bug (tracked as CVE-2026-3055) stems from insufficient input validation, which can lead to a memory overread on Citrix ADC or Citrix Gateway appliances configured as a SAML identity provider (IDP), potentially enabling remote attackers without privileges to steal sensitive information such as session tokens.
“Cloud Software Group strongly urges affected customers of NetScaler ADC and NetScaler Gateway to install the relevant updated versions as soon as possible,” the company warned in a Monday advisory.
Citrix has also shared detailed guidance on how to identify and patch NetScaler instances vulnerable to CVE-2026-3055.
The company also patched the CVE-2026-4368 vulnerability affecting appliances configured as Gateways (SSL VPN, ICA Proxy, CVPN, RDP proxy) or AAA virtual servers, which can enable threat actors with low privileges on the targeted system to exploit a race condition in low-complexity attacks, potentially leading to user session mix-ups.
The two flaws affect NetScaler ADC and NetScaler Gateway versions 13.1 and 14.1 (fixed in 13.1-62.23 and 14.1-66.59) and NetScaler ADC 13.1-FIPS and 13.1-NDcPP (addressed in 13.1-37.262).
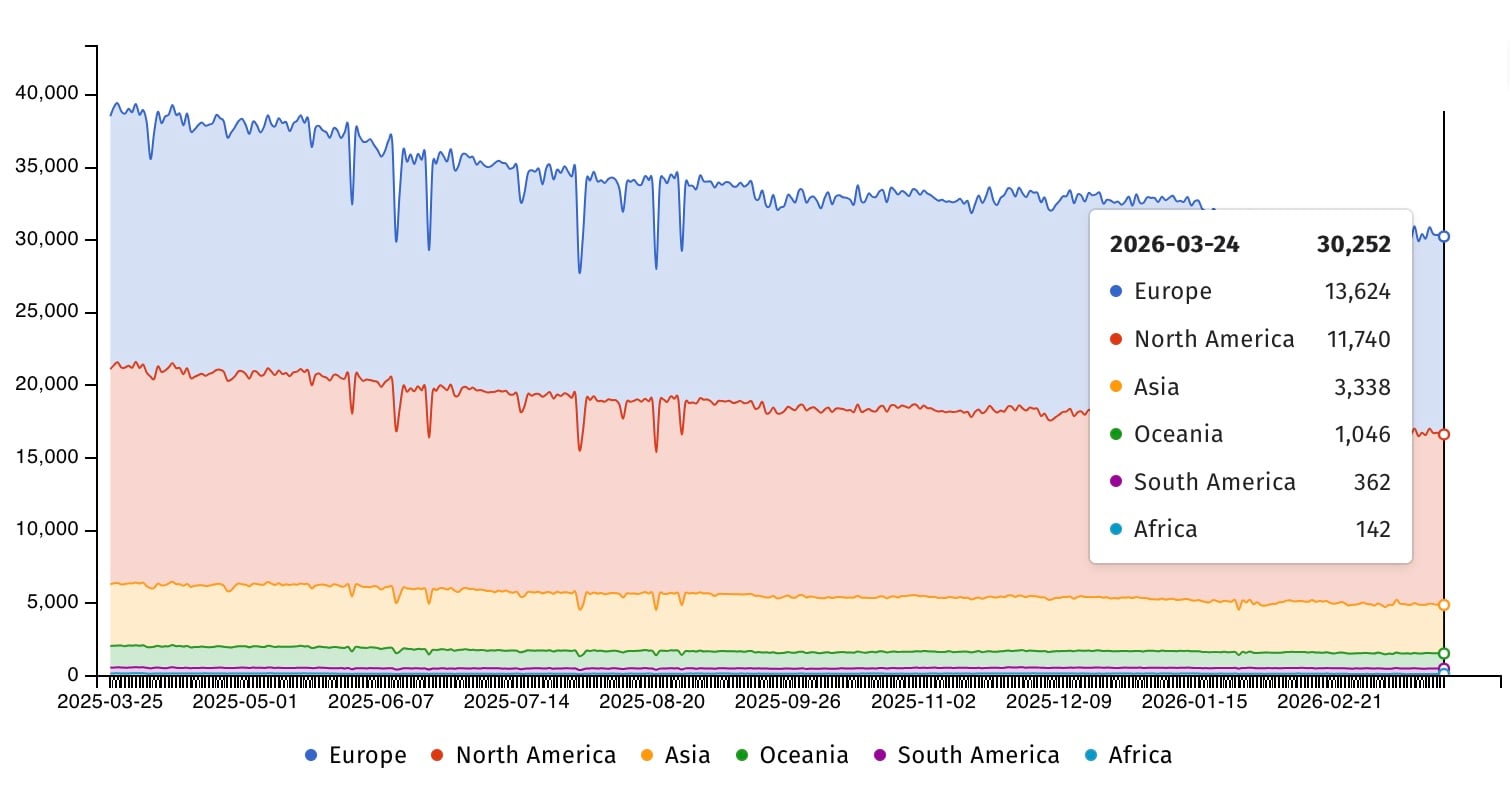
Internet security watchdog group Shadowserver is currently tracking over 30,000 NetScaler ADC instances and more than 2,300 Gateway instances exposed online. However, there is currently no information regarding how many of them are using vulnerable configurations or have already been patched against attacks.
Since Citrix released security updates to address the vulnerability, multiple cybersecurity companies have warned that it’s critical to secure NetScaler against attacks targeting CVE-2026-3055.
Many of them have also pointed out obvious similarities to the CitrixBleed and CitrixBleed2 out-of-bounds memory-read vulnerabilities exploited in zero-day attacks in recent years.
“Unfortunately, many will recognise this as sounding similar to the widely exploited ‘CitrixBleed’ vulnerability from 2023 and the subsequent ‘CitrixBleed2’ variant disclosed in 2025, both of which were and continue to be actively leveraged in real-world attacks,” cybersecurity company watchTowr said.
“Although Citrix states that the vulnerability was identified internally, it is reasonable to expect that threat actors will attempt to reverse engineer the patch to develop exploit capabilities.”
“Exploitation of CVE-2026-3055 is likely to occur once exploit code becomes public. Therefore, it is crucial that customers running affected Citrix systems remediate this vulnerability as soon as possible; Citrix software has previously seen memory leak vulnerabilities broadly exploited in the wild, including the infamous ‘CitrixBleed’ vulnerability, CVE-2023-4966, in 2023,” Rapid7 added.
In August 2025, CISA flagged CitrixBleed2 as actively exploited and gave federal agencies a single day to secure their systems. In total, the U.S. cybersecurity agency has tagged 21 Citrix vulnerabilities as exploited in the wild, seven of which were used in ransomware attacks.

