
A cybersecurity researcher has published proof-of-concept (PoC) exploits for two unpatched Microsoft Windows vulnerabilities named YellowKey and GreenPlasma, which are a BitLocker bypass and a privilege-escalation flaw.
Known as Chaotic Eclipse or Nightmare Eclipse, the researcher describes the BitLocker bypass issue as functioning like a backdoor because the vulnerable component is present only in the Windows Recovery Environment (WinRE), which is used to repair boot-related issues in Windows.
The latest exploits follow the researcher’s previous disclosure of the BlueHammer (CVE-2026-33825) and RedSun (no identifier) local privilege escalation (LPE) as zero-day flaws, both of which began to be exploited in the wild shortly after being publicly disclosed.
As in previous cases, the researcher stated that the decision to publicly disclose the YellowKey and GreenPlasma vulnerabilities, along with guidance on how to leverage them, was driven by dissatisfaction with Microsoft’s handling of bug reports.
Chaotic Eclipse, or Nightmare-Eclipse on GitHub, said that they will keep leaking exploits for undocumented Windows vulnerabilities, even promising “a big surprise” for the next Patch Tuesday.
The YellowKey BitLocker bypass
The researcher says that YellowKey is a BitLocker bypass that affects Windows 11 and Windows Server 2022/2025. It involves placing specially crafted ‘FsTx’ files on a USB drive or EFI partition, rebooting into WinRE, and triggering a shell by holding down the CTRL key.
Additionally, the BitLocker bypass should also work without an external storage by copying the files to the EFI partition on the target drive.
According to Chaotic/Nightmare Eclipse, the spawned shell gains unrestricted access to the storage volume protected by BitLocker.
Independent security researcher Kevin Beaumont confirmed that the YellowKey exploit is valid and agreed that BitLocker has a backdoor. He recommended using a BitLocker PIN and a BIOS password as a mitigation.
In an update today, Chaotic Eclipse said that “the real root cause is still not unknown [sic] by the general public” and that the vulnerability is exploitable even in a TPM (Trusted Platform Module) and PIN environment. However, the exploit for this version has not been released.
“I think it will take a while even for MSRC to find the real root cause of the issue. I just never managed to understand why this vulnerability is sooo well hidden,” the researcher said.
“No, TPM+PIN does not help, the issue is still exploitable regardless, I asked myself this question, can it still work in a TPM+PIN environment ? Yes it does, I’m just not publishing the PoC, I think what’s out there is already bad enough.”
Will Dormann, principal vulnerability analyst at Tharros Labs, also confirmed that the YellowKey exploit worked with the FsTx files on a USB drive but could not reproduce the bug using the EFI partition.
He explained to BleepingComputer that “YellowKey exploits NTFS transactions in combination with the Windows Recovery image. This PIN prompt happens before Windows Recovery is entered.”
Dormann clarified the exploit process, saying that to boot Windows Recovery, “Windows looks for \System Volume Information\FsTx directories on attached drives, and will replay any NTFS logs.”
“The result of this is that the X:\Windows\System32\winpeshl.ini is deleted, and when Windows Recovery is entered, rather than launching the actual Windows Recovery environment, it pops up a CMD.EXE. With the disk still unlocked” – Will Dormann
By default, TPM-only BitLocker configurations unlock encrypted drives automatically without requiring user interaction. If a system can transparently decrypt a disk for convenience, it is reasonable to expect that attackers may eventually find ways to abuse that process.
“YellowKey is an example of an exploit for such a weakness,” Dormann said, explaining that because it leverages the auto unlock feature on boot, the current YellowKey exploit does not work in a TMP+PIN environment.
It is worth noting that testing YellowKey with a BitLocker-protected drive must be performed on the original device, where the TPM stores the encryption keys.
As such, Chaotic Eclypse’s current YellowKey exploit does not work with stolen drives but allows access to disks that are protected with TPM-only BitLocker without needing credentials.
The GreenPlasma exploit
GreenPlasma is a privilege escalation security issue that could be exploited to obtain a shell with SYSTEM permissions. Chaotic Eclipse describes it as a “Windows CTFMON Arbitrary Section Creation Elevation of Privileges Vulnerability.”
An unprivileged user can create arbitrary memory-section objects within directory objects writable by SYSTEM, potentially allowing manipulation of privileged services or drivers that trust those locations.
The leaked PoC is incomplete, though, and lacks the component needed to achieve a full SYSTEM shell. Nevertheless, “if you’re smart enough, you can turn this into a full privilege escalation,” Chaotic Eclipse says.
The disgruntled researcher added that the newly created section could be influenced to manipulate data and various services, including kernel-mode drivers, into trusting specific paths that standard users cannot access.
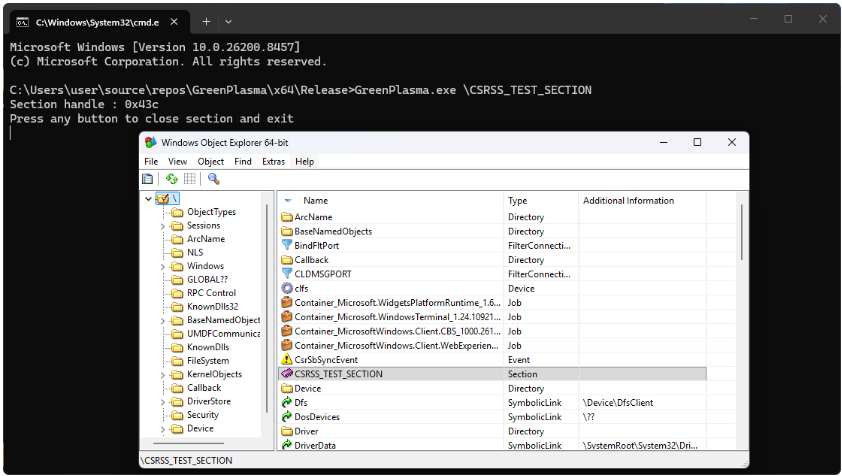
Source: GitHub
While the exact circumstances that triggered Chaotic Eclipse’s spree of exploit leaks remain unclear, the researcher has hinted at “a big surprise” for Microsoft on next month’s Patch Tuesday.
Additionally, they said that “Microsoft silently patched the RedSun vulnerability” and criticized the company for the hushed activity and not assigning an identifier for the vulnerability, as was the case with BlueHammer.
BleepingComputer has contacted Microsoft for a comment on Chaotic Eclipse’s latest exploit leaks, and a spokesperson stated that the company is committed to investigating reported security issues, “and update impacted devices to protect customers as soon as possible.”
“We also support coordinated vulnerability disclosure, a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community,” a Microsoft spokesperson told BleepingComputer.
AI chained four zero-days into one exploit that bypassed both renderer and OS sandboxes. A wave of new exploits is coming.
At the Autonomous Validation Summit (May 12 & 14), see how autonomous, context-rich validation finds what’s exploitable, proves controls hold, and closes the remediation loop.

